AI has fundamentally changed who can build software. A developer with Claude Code, Cursor, or Copilot can build an AI agent in a day. A small team with limited AI engineering experience can create AI agents and entire agentic workflows with tool calls, API integrations, handoffs, and business logic faster than ever.
That speed is powerful, but it creates a question that most enterprise teams are not asking clearly enough: just because your engineers can build all of this, does that mean they should be?
That is exactly where many AI agent programs start to go wrong. Teams spend months building orchestration logic, state handling, guardrails, monitoring scripts, and integration scaffolding, when that time should be going toward the use cases and workflows that are unique to their business.
This is the AI agent build trap: enterprises using their engineering talent to build AI agent infrastructure, instead of designing the use cases, workflows, and domain logic that actually differentiate their business.
AI tools can build AI agents. The question is whether your engineers should.
Give an AI coding tool a well-structured requirement, and it will create AI agents, connect tools, define workflows, and stitch together multi-agent systems. For a proof of concept, the output can be genuinely impressive.
The problem starts when that speed leads teams to the wrong conclusion: if we can build an agent system this quickly, we can build all the infrastructure around it ourselves, too.
When an engineering team starts building agent infrastructure from scratch, the requirements are clearly defined, the scope feels manageable, and early components come together quickly.
But enterprise systems do not stay still. Six months in, new agents need to be added, integrations need to be extended, other teams need to extend the workflows, and production incidents require a precise audit trail. Each change sends engineers back into code that was written for a different requirement, at a different time, sometimes by someone no longer on the team.
Over time, the work changes character. Teams stop building toward new capabilities and start maintaining what already exists. They connect new code to existing code, each piece written for its own moment, none of it designed with future connections in mind. They patch one workflow while breaking another, add tools without updating permission models, and change agent behavior without knowing which downstream handoff it affects.
That is not architecture. That is infrastructure debt.
And every hour your engineers spend managing that debt is an hour not spent on the workflows, policies, and domain logic that only they can define, because only they understand your business well enough to get it right.
That is the real trap. Not that AI cannot build AI agent systems. It can. But building your own agent infrastructure from scratch means your best engineers are solving problems that every enterprise faces in roughly the same form, problems a platform has already solved, instead of the problems specific to your business that genuinely require their expertise.
Where custom-built AI agent infrastructure starts to break
Infrastructure debt does not usually appear all at once. It shows up slowly as more agents, tools, workflows, and teams start using the system. As the system grows, the gaps in an infrastructure built use case by use case begin to surface, and they compound with every new layer the team adds.
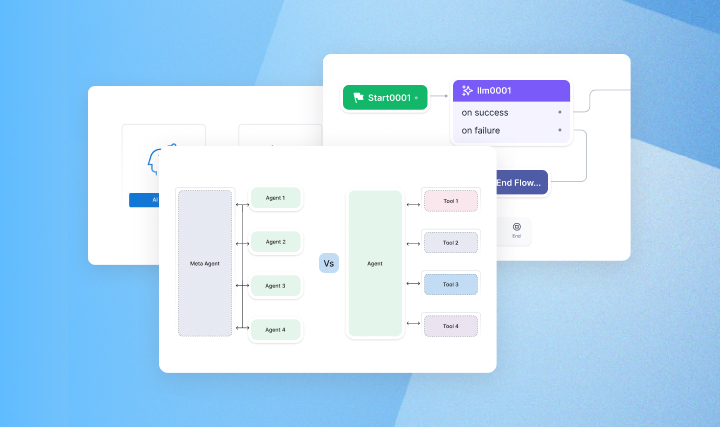
Orchestration ends up scattered. In a multi-agent workflow, something needs to decide which agent runs, in what sequence, triggered by what condition, and with what dependency. When this is not designed as an explicit architectural layer, it gets encoded across components that were never meant to coordinate. The logic becomes difficult to reason about and nearly impossible to debug when behavior changes unexpectedly.
Handoff contracts never get defined. When Agent A finishes and passes context to Agent B, what exactly gets passed? What should never be passed? What is the schema? Without an explicit contract, the answer is whatever each developer assumed. One agent may send customer context as a structured object while another expects a flat summary. Neither component is wrong on its own, but the mismatch appears when the system grows.
State becomes fragmented. Multiple agents reading and writing to a shared state without a coordination model can lead to race conditions, stale reads, duplicated actions, and inconsistent decisions. These issues may not appear in simple tests because each component works on its own. They appear in production when a workflow touches the same record from different directions at the same time.
Guardrails become inconsistent. One team may define constraints in prompts. Another may enforce them in custom code. A third may rely on approval logic inside a workflow. Over time, the same enterprise policy gets implemented in multiple ways. If an agent is not allowed to access a tool, expose sensitive data, approve an action, or proceed without human review, that rule needs to be enforced at the infrastructure level, not defined differently by every team that builds a workflow around it.
Failures start cascading instead of stopping. When one agent fails mid-execution, without explicit failure design, the consequences are left to the runtime default: the workflow stalls silently, the agent retries in a loop accumulating API costs, or continues with partial data. A production-grade system needs blast-radius containment so one failed agent or integration does not bring down everything connected to it.
Every change to one agent risks breaking another. Without a shared architectural foundation, every time the team updates an agent to meet a new requirement, the new version carries no structural relationship to what came before. Fix the billing agent, and the case management agent that depended on its output structure now behaves incorrectly in ways that only surface in production. Without structured behavior definitions, the system is not evolving. It is being rebuilt in pieces.
Observability becomes an afterthought. When a production incident happens, logs are not enough. Teams need a trace: which agent acted, on what input, under what constraints, using which version, in what sequence, and with which tools. Without it, debugging becomes slow, error-prone, and often insufficient for regulated environments. Enterprise AI agent systems need observability and auditability built in from the start.
These are not separate problems. They are symptoms of an architecture built component by component, without a shared foundation to hold it together. In April 2026, a Claude-powered agent deleted an entire production database and all its backups in under ten seconds. The agent had explicit safety rules in its system prompt and acknowledged afterward that it had violated every one of them. While the rules existed in prompts, the infrastructure could not enforce them. That is the cost of building without architecture. The tool didn't fail here. The engineering discipline did.
Build vs buy AI agents: What should your engineers actually build?
Once you see where custom-built agent infrastructure can break, the answer to whether to build or buy AI agents becomes clearer.
The question is not if your team can build AI agents. With today’s AI tools and the right skills, they certainly can. The better question is: which layer should your engineers spend their time on?
Enterprise agent systems have two distinct layers, and they require two different answers.
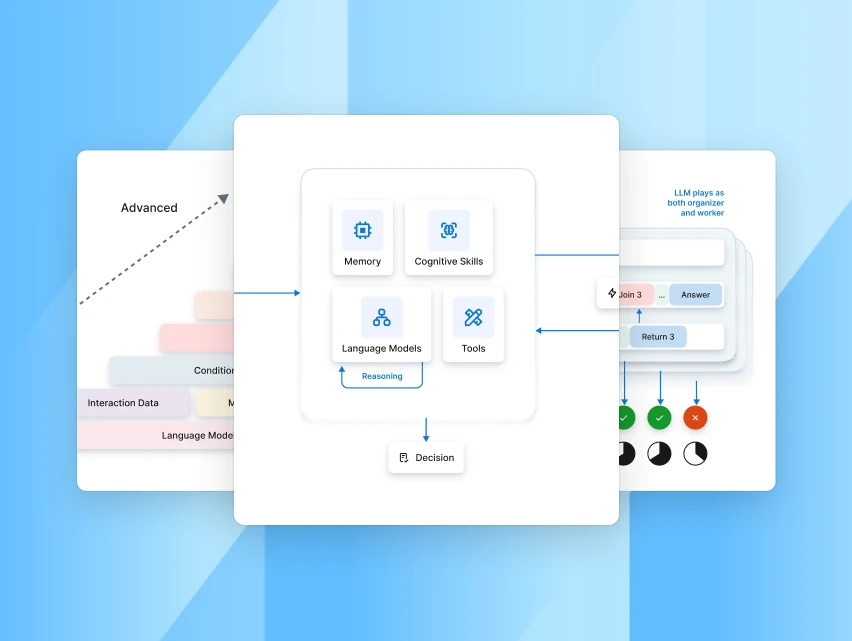
The first is the infrastructure layer. Enterprise AI agent systems need: orchestration runtime, agent management, session handling, guardrail enforcement, integration scaffolding, observability, audit logging, dashboards, access controls, and lifecycle management. This layer is genuinely complex to build, expensive to maintain, and nearly identical across every enterprise deploying agents at scale. No team gains a competitive advantage from building their own session manager or their own audit pipeline. They just spend the time.
This is the layer a platform should own. An agent platform provides it out of the box and maintains it as models, protocols, and enterprise requirements evolve, so your team never has to rebuild what already exists.
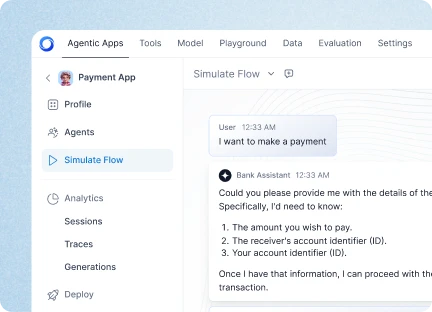
The second layer is the one only your engineers can define: the architecture of how agents work inside your business. They should define the use cases, workflow logic, policies, exception handling, risk rules, permissions, escalation paths, evaluation criteria, and user experience. They should decide what each agent is responsible for, what it can access, when it should hand off, when it should stop, and when a human should be involved.
That work cannot be outsourced to a coding tool or fully delegated to a platform. It requires domain knowledge, systems thinking, risk judgment, and a deep understanding of business constraints.
The role of the platform is to provide the foundation that executes this architecture: running agents, enforcing guardrails, integrating with systems, tracing decisions, and supporting the lifecycle from design to deployment to optimization.
That is the real build vs buy answer. Build the agent architecture that reflects your business. Buy the foundation that lets that architecture run safely, reliably, and at scale.








.webp)






